
Watch or listen to just about any VPN ad, and it will make huge claims. VPN companies love to promise that by using their service, you’ll be protected from malware, identity theft, and prying eyes. As a result, many people think a VPN is a must-have to ensure that they’re protected while browsing the internet.
VPNs have their uses, but they’re not the ultimate security or privacy tool that these ads would have you believe. No matter how good the price, there are a few important things you should keep in mind when choosing a VPN provider.
Let’s bust some common VPN myths and dive in on how you can determine if a VPN is right for you.
What is a VPN?
Let’s begin by defining two terms: VPN and encryption. VPN stands for Virtual Private Network. VPNs are secure digital tunnels your web traffic can travel through when flying across the internet. People use VPNs to prevent untrusted third parties from seeing their web traffic and to bypass geo-restrictions. More on that in the use case section. A VPN is similar to an actual tunnel in that no one on the outside can see your car while driving through it. All they see is the tunnel.
The secure part of “secure digital tunnels” is done by leveraging a technology called encryption. Encryption is a process which scrambles data into an unreadable format to unauthorized third parties. In the case of our actual tunnel analogy, encryption is like gates on either side of the tunnel. Unless you have a key to unlock the gates (authorized party), you can’t view who’s driving inside (your data).
Use case: Business Infrastructure
Secure remote access to corporate resources is the original use for a VPN. VPNs were created by a team at Microsoft who developed the Point-to-Point Tunnelling Protocol (PPTP) to remotely connect to corporate resources in a secure way. Many organizations have critical confidential resources secured behind firewalls. Consider a healthcare provider with medical records, banks with financial data, or a corporate executive with trade secrets. Traditionally, the only way to access the resources behind a firewall was to be physically present in the local office and be connected to the network hosting these resources.
However, even before remote and hybrid work became popular, there was a growing need to securely access corporate resources outside the office, often by travelling executives or sales team members. The need to remotely access secured resources ballooned during the COVID-19 pandemic, where offices globally had to shut down, and nearly every white-collar job had to be done from home.
Corporate VPNs like Cisco AnyConnect are downloaded to an employee’s computer. After authenticating with a username and password, they can securely access corporate resources anywhere in the world. Corporate VPNs are one of the most common and practical uses for VPNs. However, with the rise of Software-as-a-Service (SaaS) and Zero-Trust Network Access (ZTNA), corporate VPNs are slowly finding themselves replaced with more modern solutions.
Use case: Security
With the growing threat of malware like ransomware and compromised accounts caused by phishing attacks, VPN providers love to suggest that their products protect against such threats. However, it’s a myth. Most VPNs do not protect against malware, phishing attacks, or unsafe websites. After all, VPNs are just fancy digital tunnels, not content filters or malware scanners.
Nevertheless, VPNs can help to protect against one specific type of cyber threat: Man-in-the-middle (MITM) attacks. MITM attacks are most often conducted on public Wi-Fi networks. They are where an attacker can intercept another’s internet traffic. Most of the time, MITM attackers monitor this traffic for potentially sensitive data. However, in some situations, attackers can alter transmitted data before it’s sent to the receiver.
MITM attacks aren’t as common as they used to be, though. Most websites are protected by HTTPS or Hypertext Transfer Protocol Secure. You know a website is encrypted by HTTPS when you see a little lock icon in your browser. HTTPS dramatically changed what data was being sent openly over the internet. VPN ads often suggest that your passwords and credit card data are sent insecurely across the internet, which is true if a website isn’t leveraging HTTPS. But you’d have difficulty finding a legitimate website accepting passwords and credit cards that don’t use HTTPS.
It’s important to remember that VPNs are not a one-all security tool. Suppose you are concerned about malware or phishing attacks. In that case, you’re better off investing in good anti-malware software and some phishing awareness training. However, if you’re on a public Wi-Fi network, like at a hotel while travelling or working remotely at Starbucks, it doesn’t hurt to use one even though you likely don’t need it. Personally, I do use a VPN on public networks, mainly for peace of mind or my mobile data for better speed.
Use Case: Privacy
Privacy is a big one regarding the appeal of using a VPN, but the answer might be a little more mixed than you first thought. Before HTTPS, most of what you did on a website was openly viewable on the internet. However, since the widespread implementation of HTTPS, very little data is actually transmitted unencrypted: your IP address, the website you’re visiting (the domain name), and metadata such as date, time and duration of the website visit.
At first glance, you might be angry about how much data is being shared unencrypted. But remember, your internet service provider (ISP) like Bell, Telus, Rogers, or Eastlink needs to send you wherever you’re looking to go on the internet. Your IP address is also used to approximate your location, which can be helpful when trying to find local restaurants or businesses.
VPNs can nicely complement HTTPS because they conceal your unencrypted metadata from your ISP, network administrator, or MITM attackers. Hiding metadata is very attractive for journalists, political dissents, or those in regions where accessing certain content may be illegal. In Canada, while our ISPs are not always the most upstanding organizations, they are not selling our internet usage to advertisers or manipulating traffic speeds to prioritize one service over another.
Using a VPN at home to prevent your ISP from viewing your metadata is not worth it. You’ll likely become more frustrated due to speed throttling and lack of geo-specific search results than the privacy benefits you’d gain. However, if you’re in a region where specific content is blocked that you need to access, such as in China and social media like Facebook or Twitter, or you’re an international reader, and your ISP sells your web traffic data or throttles access to certain websites, then a VPN can be a helpful service.
Use Case: Geo-restrictions
Bypassing geo-restrictions is likely the most popular consumer use for VPNs. Since VPNs mask your IP with their own, you can appear to be coming from anywhere in the world. Going back to the actual tunnel analogy from earlier, imagine that this tunnel is so long that it connects to many different places. So many, in fact, that you can claim you’re coming from just about anywhere when you’re coming out of the tunnel, and the border guard wouldn’t know if you’re telling the truth or not.
 This assumption happens when you use a VPN to access another country’s Netflix catalogue or geo-restricted YouTube content. The United States and Canada have two of the largest Netflix catalogues in terms of quantity, but that doesn’t always mean the content you want to watch is available there. Similarly, some content I watch on YouTube is geo-restricted to a U.S.-only audience.
This assumption happens when you use a VPN to access another country’s Netflix catalogue or geo-restricted YouTube content. The United States and Canada have two of the largest Netflix catalogues in terms of quantity, but that doesn’t always mean the content you want to watch is available there. Similarly, some content I watch on YouTube is geo-restricted to a U.S.-only audience.
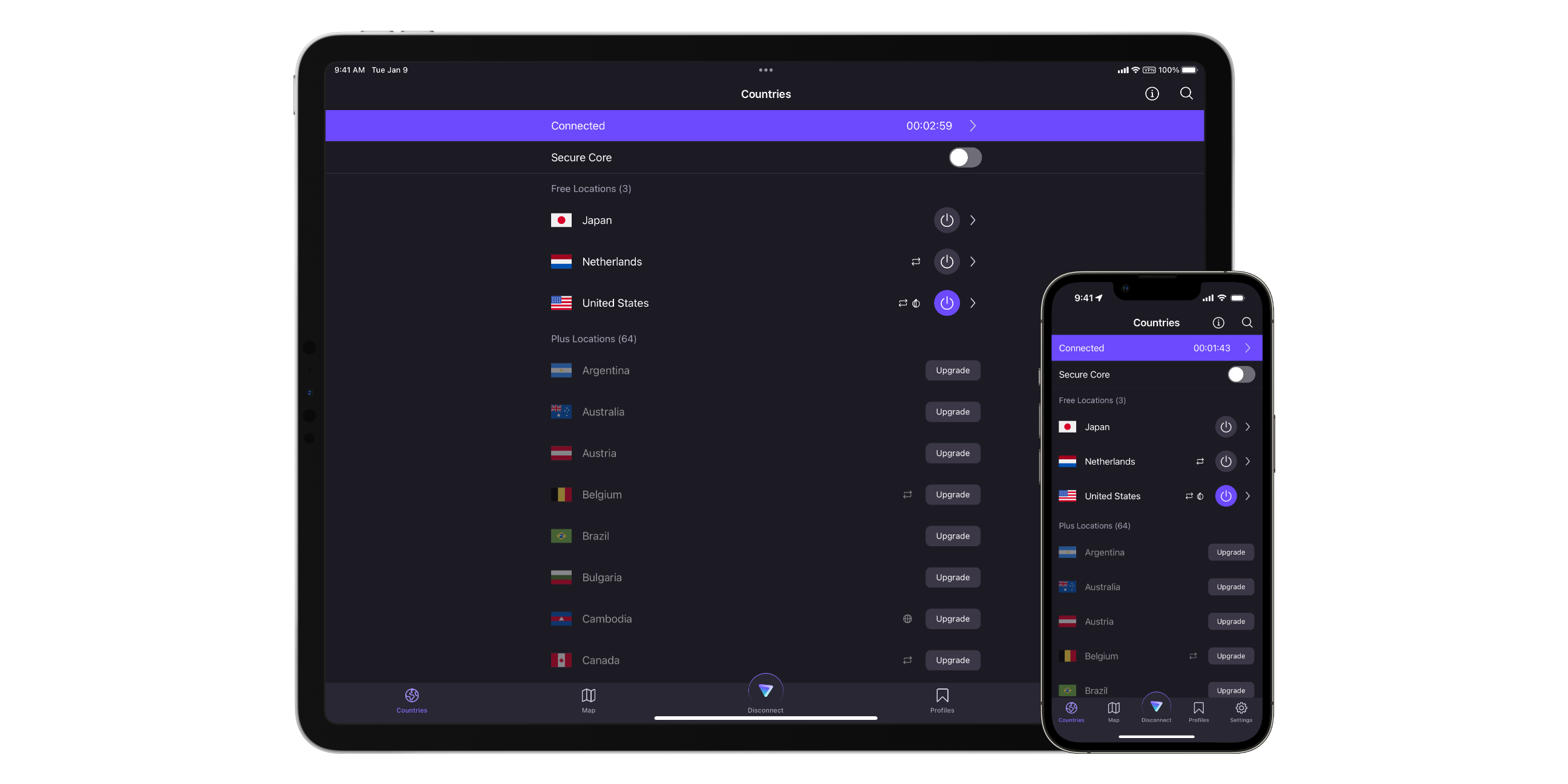
VPNs allow users to select the country they want to appear to be coming from to access the content library of choice. This strategy works in reverse too. If you’re travelling outside of your home country, you may want to use a VPN to get access to content only accessible via your native country’s library.
VPN considerations
 Now that you’ve read through the top four use cases for VPNs, let’s assume you’re now determined to subscribe to one. Yet, there are so many of them. Which one do you pick? Here is a list of top potential factors to consider:
Now that you’ve read through the top four use cases for VPNs, let’s assume you’re now determined to subscribe to one. Yet, there are so many of them. Which one do you pick? Here is a list of top potential factors to consider:
1. Good security: This probably goes without saying, but you want to ensure your VPN uses industry-standard security practices. There are many buzzwords regarding security, so you may have to use your best judgment here. At the very least, make sure your VPN uses 256-bit or “military-grade” encryption.
2. Server locations & performance: If you’re using a VPN to avoid geo-restrictions, ensure the VPN you subscribe to offers servers within the region to which you need to connect. Additionally, watch out for massive speed cuts when using a VPN. Performance drops are common when using a VPN because your data has to travel further. Take advantage of free trials to make sure the performance meets your needs.
3. Device compatibility: Make sure that when selecting a VPN, you pick one that supports the operating systems you use. Most VPNs support all major operating systems; however, some services, like Netflix and Disney+, won’t let you stream content via their iOS apps when running a VPN. Keep these limitations in mind before spending big bucks on a VPN.
4. Privacy, pricing & customer support: Let me be clear — most free VPNs are very bad. When you aren’t paying for a product, you most likely are a product. Remember that while your ISP or network administrator may not be able to see your web traffic metadata when using a VPN, your VPN provider still can.
Therefore, selecting a VPN with a strong privacy policy is very important. Ideally, the VPN provider has a strict zero-log policy meaning they do not retain any of your browsing traffic. This is particularly important when using a free VPN since they likely profit from selling your internet traffic data to advertisers. When picking a VPN, you have to trust your VPN provider more than you trust your ISP, network administrator, or government. After all, you’re now funnelling all your network traffic through them, so if the VPN provider isn’t trustworthy, it makes for a poor privacy tool.
It’s also important to remember that while VPNs mask your IP address from trackers, they don’t block all trackers either. Advertisers and websites have many different ways to track you across the internet. So, again, VPNs aren’t a one-stop shop for preventing trackers either.
Choosing a good VPN doesn’t have to be crazy expensive, either. Pricing sensitivity is based on the wallet of the spender. Generally, a paid VPN is more trustworthy than a free one. However, take all this into account and do some price comparison. Make sure you’re getting a good deal based on the uses that you’ve identified for yourself. Free trials are great, but only if the customer service experience is there to back it up.
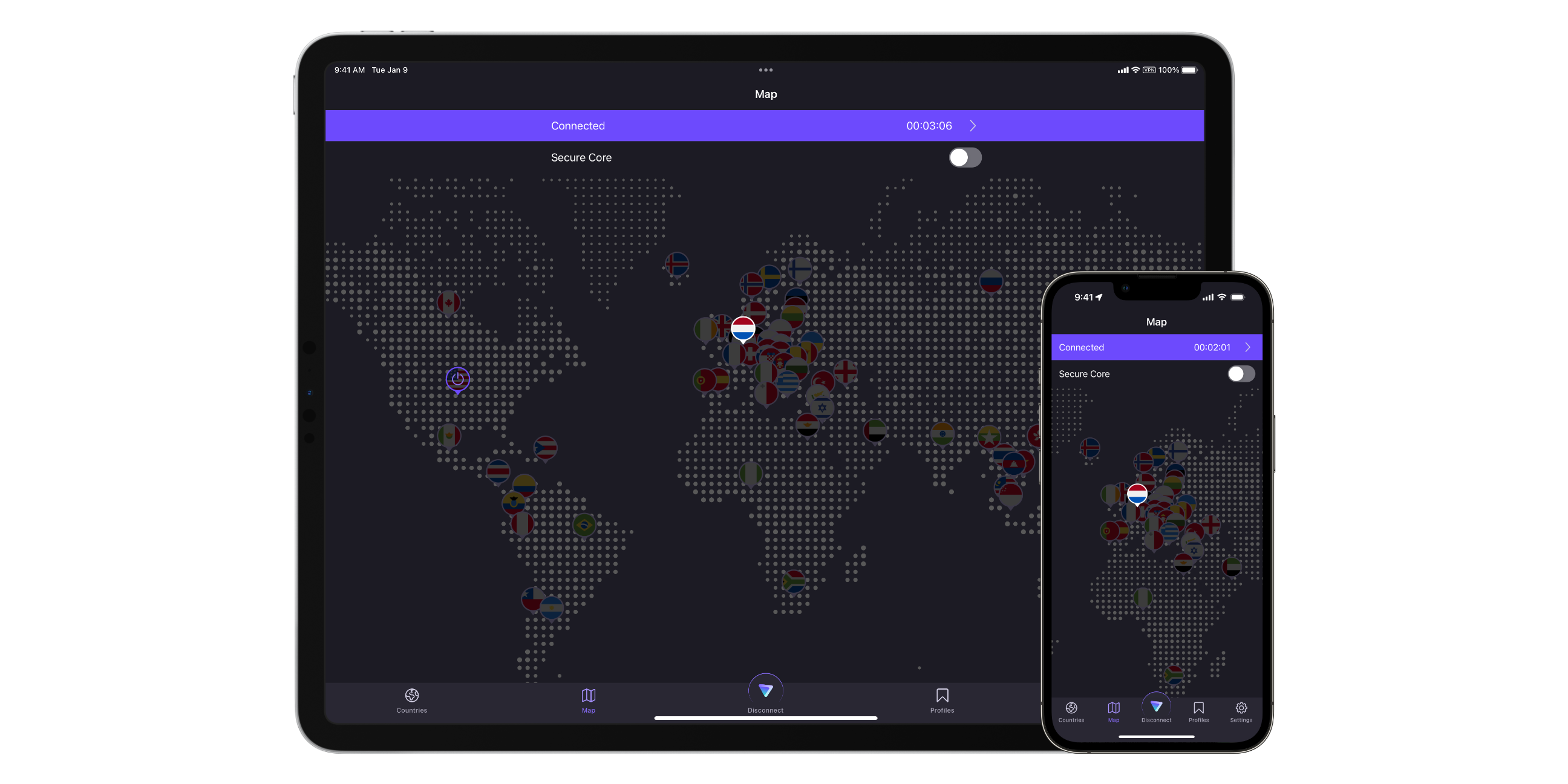
Personally, I rarely use a VPN because I work from home and trust my ISP (at least in this context). However, when I opt to connect to a public Wi-Fi network instead of using my cellular data or need to change my location to avoid the occasional geo-restriction, I use the free tier of ProtonVPN.
ProtonVPN offers the best free tier I’ve seen. While it doesn’t provide the fastest speeds or the most flexibility in terms of international servers, it does provide unlimited usage and support for macOS and iOS, my operating systems of choice.
ProtonVPN is also ad-free, with a strict zero-logs policy and has the core benefit that privacy is a human right. If I needed more from my VPN, I’d likely subscribe to ProtonVPN. This isn’t an ad but an open recommendation based on what I currently use at the time of writing. When choosing a VPN, identify your personal use case(s), do some research, and find the best service that meets your needs.
MobileSyrup may earn a commission from purchases made via our links, which helps fund the journalism we provide free on our website. These links do not influence our editorial content. Support us here.


